Ladies and gentlemen, repeat after me:
Electronic/internet voting is a bad idea because of remote unauthorized access.
Electronic/internet voting is a bad idea because of remote unauthorized access.
Electronic/internet voting is a bad idea because of remote unauthorized access.
Electronic/internet voting is a bad idea because of remote unauthorized access.
Electronic/internet voting is a bad idea because of remote unauthorized access.
Electronic/internet voting is a bad idea because of remote unauthorized access.
Good this this was just a test and not the real thing! *shudders*
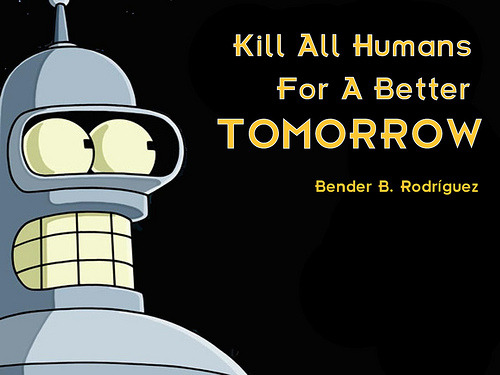
http://pcworld.co.nz/pcworld/pcw.nsf/news/hackers-elect-futuramas-bender-to-the-washington-dc-school-boardThis was not some nefarious attack from a group of rouge hackers: The DC school board actually dared hackers to crack its new web-based absentee voting system four days ahead of the real election. University of Michigan professor Alexander Halderman, along with two graduate students, did the deed within a few hours.
A full account of the hack is here:
https://jhalderm.com/pub/papers/dcvoting-fc12.pdfLet’s list all the failures put forth by the article:
Fail #1
After looking over the e-voting system's Ruby on Rails software framework…
Don’t use Ruby on Rails, it is filled with drama and incompetence. The GitHub drama
http://chrisacky.posterous.com/github-you-have-let-us-all-down proved this beyond reasonable doubt.

Also dongs,
https://github.com/nickmartini/dongml,
http://sheddingbikes.com/posts/1306816425.html.
Fail #2
While the hackers were mucking about the system's server, they discovered other files that were not ballot-related in the /tmp/ directory. Among them was a 937-page PDF containing instructions to individual voters as well as authentication codes for every voter.
When the team tried to get into the terminal server, they noticed there was an attack coming from Iran; they traced the IP address to the Persian Gulf University. The team realised the Iranians were getting in with one of the default admin logins (user: admin, password: admin). To stop the outside attacks the team blocked the offending IP address with iptables (a piece of software for server admins) and replaced the admin password with something more challenging. The team also blocked similar attacks launched from New Jersey, India, and China.
Basic system administration, how does it fucking work?